Tracking A Cell Phone Location
Using Cellular Technology To Locate Criminals
For years, police departments and government agencies have called upon a vast array of technological gadgets and gizmos to uncover criminal activity. These items have included hidden cameras, wiretaps, GPS tracking systems, and more. However, some forms of surveillance technology have been met with a high level of criticism, and some applications have been so controversial that they had to be evaluated by the high courts. This was the case of police using tracker devices without warrants to track down where potential criminal suspects would travel in their personal automobiles. Although the proper protocol for police use of GPS monitoring systems is now in place, the law enforcement use of cellular towers to determine locational data of potential suspects is still a very large concern for privacy advocates, police departments, and attorneys everywhere.
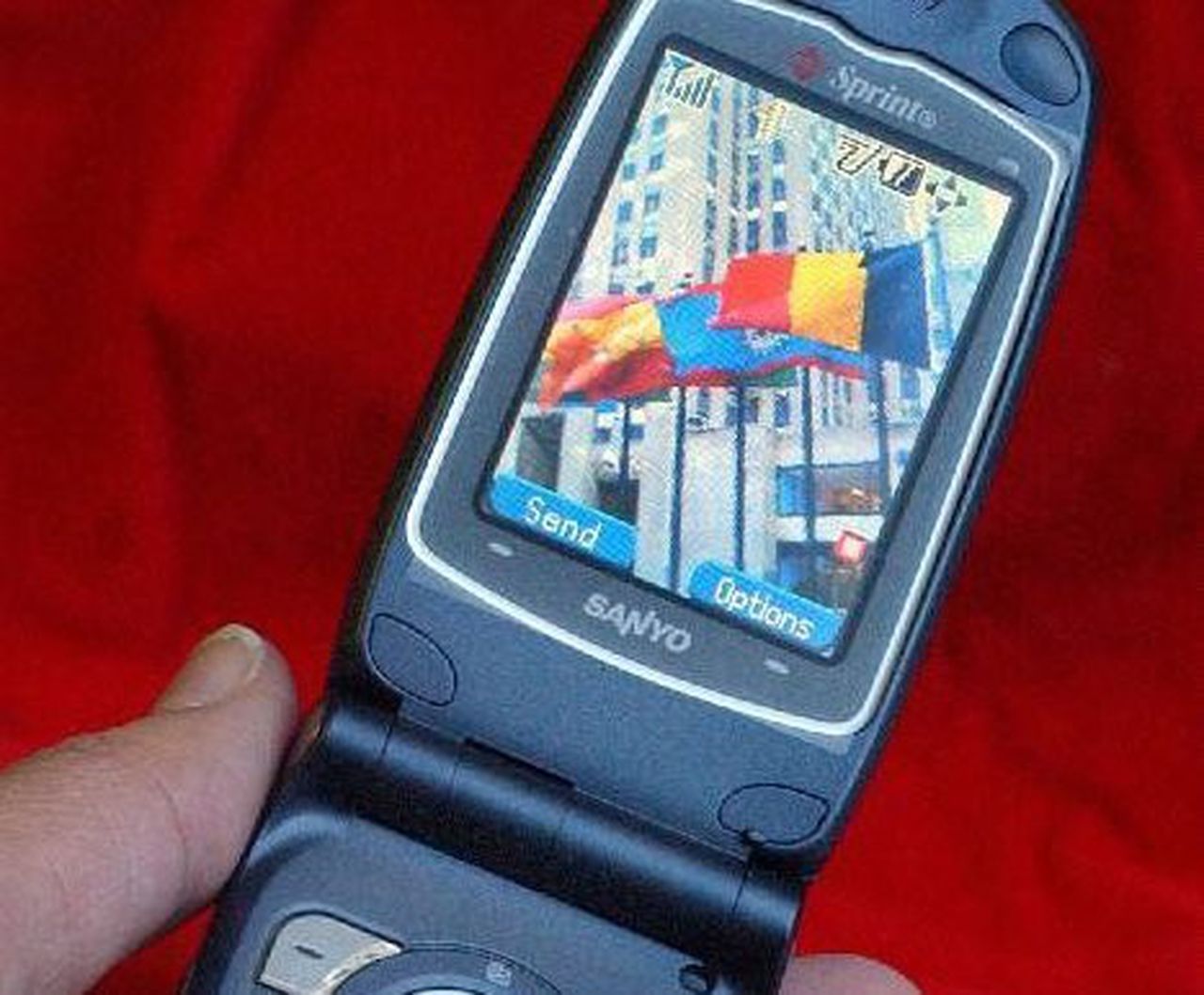
Cell phones are incredible pieces of technology that allow people to place and receive phone calls, check emails, connect with friends through social networking, and more, but these devices are also data farms that even store information regards to locational data. Basically, this means cell phones are storing every place a person goes, how long they were at specific locations, and more. This is done through the use of the GPS monitoring chip manufactured in every mobile phone and cell tower.
How To Ping A Cellphone Without Permission
In modern parlance and cellphone slang terms, to ping a phone is technically to send a simple packet to a network interface and then receive an echo reply. Its actually a digital version of what bats and dolphins do as part of echolocation.
But if you actually want to discover a particular users or particular phones exact location, that can also be termed pinging. The reasons for pinging are varied some wish to meet up with a friend but arent able to, while police stations and detective agencies use legal software to ping cellphones and track down perpetrators and suspects.
The most detailed pinging, including the exact GPS location, phone number, and persons name connected to the cellphone, are only available via authorized software that only a select few are allowed to access. Lets look deeper into how to ping a cellphone without permission.
Court: Police Have To Get A Warrant To Ping A Cell Phone
adamgTue, 04/23/2019 – 12:01pm
And one of those reasons would be a manhunt for a man police believed had just murdered somebody with a sawed-off shotgun, the Supreme Judicial Court ruled today.
In a ruling on a 2012 murder in Brockton, the state’s highest court first said that police normally would need a warrant to ask a wireless provider to “ping” a phone, which could reveal its location via GPS, because pinging constitutes the sort of a search covered by the Fourth Amendment and the equivalent section of the state constitution.
But, the justices continued, as with all other searches, there are certain “exigent circumstances” under which police can seek a ping without a warrant if they can show sufficient probable cause for the search.
At the same time, three justices said the case shows it’s past time for the state legislature to pass a law that would let police seek a search warrant from a judge electronically when time is of the essence, rather than requiring a hearing in person.
In the case at question, police were looking for Jerome Almonor, whom they suspected of shooting a man in the chest with a sawed off shotgun on August 10, 2012. Within four hours of the discovery of the dying victim, police had IDed Almonor – who has yet to come to trial – as as a suspect and had obtained his cell number, which they asked his phone provider to ping, according to an SJC summary.
Also:
And so:
Read Also: How To Become A Police Officer In Oklahoma City
Can I Ping A Cell Phone
cell phonepingcellphone’scan docell phonephone
. Correspondingly, can you ping someone’s phone?
Locator Pings.When a locator ping is sent to a phone running Family Tracker, the phone’s position will be forced to be updated immediately, without any user’s intervention or notifications. Note – On Android phones the location updates will occur immediately even if the user does not hear/accept the ping requests.
Additionally, how can I find someones location using their cell phone number? To get real-time results, IMEI & GPS call trackers can be used to track the location of a phone call. Apps like GPS Phone& Locate Any Phone are great with tracking mobile phones, even when the phone is not connected to the internet. You can know the GPS coordinates of a phone number within seconds.
Accordingly, how do I ping someone?
To run a ping, open the command prompt by pressing “Windows-R” and entering “cmd.” At the prompt, type “ping” without quotes, enter a domain name, such as “google.com” and press “Enter.” The tool sends several pings and displays how long each takes to return. If the ping fails, try using an IP address, such as “64.233.
Can you ping a cell phone to find its location?
Do Stingrays And Dirtboxes Have Other Capabilities

Stingrays and dirtboxes can be configured for use in either active or passive mode. In active mode, these technologies broadcast to devices and communicate with them. Passive mode involves grabbing whatever data and communication is occurring in real time across cellular networks without requiring the phone to communicate directly with the interception device. The data captured can include the IMSI number as well as text messages, email, and voice calls.
If that data or communication is encrypted, then it would be useless to anyone intercepting it if they dont also have a way to decrypt it. Phones that are using 4G employ strong encryption. But stingrays can force phones to downgrade to 2G, a less secure protocol, and tell the phone to use either no encryption or use a weak encryption that can be cracked. They can do this because even though most people use 4G these days, there are some areas of the world where 2G networks are still common, and therefore all phones have to have the ability to communicate on those networks.
The versions of stingrays used by the military can intercept the contents of mobile communications text messages, email, and voice calls and decrypt some types of this mobile communication. The military also uses a jamming or denial-of-service feature that prevents adversaries from detonating bombs with a mobile phone.
Don’t Miss: How To Find Police Report Number
Can The Devices Be Used To Infect Phones With Malware
Versions of the devices used by the military and intelligence agencies can potentially inject malware into targeted phones, depending on how secure the phone is. They can do this in two ways: They can either redirect the phones browser to a malicious web site where malware can be downloaded to the phone if the browser has a software vulnerability the attackers can exploit or they can inject malware from the stingray directly into the baseband of the phone if the baseband software has a vulnerability. Malware injected into the baseband of a phone is harder to detect. Such malware can be used to turn the phone into a listening device to spy on conversations. Recently, Amnesty International reported on the cases of two Moroccan activists whose phones may have been targeted through such network injection attacks to install spyware made by an Israeli company.
U.S. law enforcement use of stingrays domestically is more curtailed, given that they, unlike the military, need to obtain warrants or court orders to use the devices in federal investigations. But there is little transparency or oversight around how the devices are used by federal agents and local police, so there is still a lot that is unknown: for example, whether theyve ever been used to record the contents of mobile phone communications or to install malware on phones.
A Cell Phone Ping Is Used By Apps And Web Services
Customers can give application providers permission to access their location information it happens all the time. Facebook, Twitter, Google, and countless other apps all have location information built-in.
But these apps cant just obtain location information willy-nilly. Theres strict rules they have to follow. Plus, the expectation by the consumer is that their location information is only going to be used by that application, for purposes disclosed, and specified in the applications Terms and Conditions.
Read Also: Where Can I Buy A Police Radar Detector
To Obtain Location Information Steps Must Be Followed
Obtaining it any other way is not compliant and in violation of laws.
First, the application provider must notify a customer that the application wants to obtain their location information. Next, the customer must have the choice of agreeing or declining to allow the app to obtain their location informationbefore the app obtains their location information. If the customer agrees to allow the app to use their location information, the application must publish terms and conditions in a URL and also a telephone number that the customer can call with questions.
If the location information is ongoing, the application must remind the customer every 30 days that their location is being obtained. The application must also offer the customer a way to opt-out at anytime, while their location information is being obtained. Several recent legislation actions concern exactly how location information permission and consent can be granted, and what notices are necessary.
As I previously stated, there has to be an opt-in, a positive assent, a means to opt-out, and terms and conditions that include the use of the location information along with a privacy statement.
Virginia Police Routinely Use Secret Gps Pings To Track Peoples Cell Phones
Scott Durvin says he faced aggressive questioning from a Chesterfield County Police detective after his friend died of a drug overdose at the end of 2019. What he didnt know at the time was that police had also begun secretly tracking his whereabouts by ordering Verizon Wireless to regularly ping his phones GPS and report his location back to detectives in real-time.
Thats kind of shocking, really, Durvin said, reached by phone at the same number police were using to follow him virtually a little more than two years ago. The detective would call me all the time and try to get me to give them information and he would threaten to lock me up. But I didnt have anything to do with it and he finally left me alone.
Police never described Durvin as a suspect in the search warrant application they submitted seeking permission to track him and court records show he has not been charged with any crimes in Virginia since police took out the warrant.
Instead, officers wrote that they had found voicemails from Durvin on the overdose victims phone and thought tracking his location might help them figure out who supplied the deadly dose of heroin, noting that Durvin had been with the man during what appeared to be a prior overdose in Richmond.
The case offers a glimpse into a surveillance technique thats become commonplace for police but is mostly unknown among the general public: cell phone location tracking.
Read Also: How Can I Get My Police Report Online
Can Police Track Your Phone Canada
The grounds upon which the police may obtain a warrant to track a cell phone are found in section 492.1 of the Criminal Code of Canada.However, a recent Ontario Court of Appeal decision confirmed that the police may be able to track your cell phone without a warrant where exigent circumstances exist.
How Long Has Law Enforcement Been Using Stingrays
The technology is believed to have originated in the military, though its not clear when it was first used in combat zones or domestically in the U.S. The earliest public mention of a stingray-like device being used by U.S. law enforcement occurred in 1994, when the FBI used a crude, jury-rigged version of the tool to track former hacker Kevin Mitnick authorities referred to that device as a Triggerfish. In a case in Utah in 2009, an FBI agent revealed in a court document that cell-site simulators had been in use by law enforcement for more than a decade. He also said they werent just used by the FBI but also by the Marshals Service, the Secret Service, and other agencies. Recent documents obtained by the ACLU also indicate that between 2017 and 2019, the Department of Homeland Securitys Homeland Security Investigations unit has used stingrays at least 466 times in investigations. BuzzFeed News had previously obtained records showing that from 2013 to 2017, HSI had used the technology 1,885 times.
Don’t Miss: How To Get Police Report For Lost Passport
Law Enforcement Wants Access To Personal Data On My Phone Can They Do That
Short answer: If your phone is protected by a passcode or biometric unlocking features, theres a chance police cant gain access to your personal data. But thats not guaranteed.
Long answer: In addition to data hosted by a third party, theres a lot of information that can only be gained from access to your phone. For example, the data in iCloud backups is only as recent as the last time you uploaded it, and it only includes what you choose to give it assuming you back up your phone at all. Encrypted messaging services like WhatsApp dont store messages on their servers or keep track of who is sending them to whom, so the only way for police to access them is through the senders or the receivers device. And as weve explained above, the government can get WhatsApp messages from the person youre communicating with, but only if it knows who it is in the first place.
Essentially, the Fifth Amendment says you cant be compelled to give self-incriminating testimony. Testimony, in this case, is defined as revealing the contents of your own mind. Therefore, civil rights advocates say, the government cant force you to tell them your phones password.
Obviously, a 44-year-old decision over tax papers doesnt take into account how information can be stored today, nor how much.
The EFFs position is that the foregone conclusion exception is very narrow and should never apply in these passcode cases, Crocker said.
Several Types Of Cell Phone Spying Equipment Exist
StingRay devices have gotten the lions share of attention in recent months. The Harris Corporation, the company that makes them, has refused to give out details about the devices and warns that prosecutors could go after anyone who dares to spread certain information without permission.
In 2013, the news site ArsTechnica reported on what the StingRay is: Its a box-shaped portable device that gathers information from phones by sending out a signal that tricks them into connecting to it. The authorities can then hone in on specific phones of interest to monitor the location of the user in real time or use the spy tool to log a record of all phones in a targeted area at a particular time. StingRays can also eavesdrop on conversations, ArsTechnica says. In 2013, they cost $68,479 or $134,952, depending on the version.
ArsTechnica says there are plenty of other devices that do similar things, including another portable device called Gossamer also manufactured by Harris Corporation that cost $19,696. The FBI spent more than $1.3 million on the technology in the 2000s.
Several American police departments, meanwhile, have bought Hailstorm systems from Harris that could cost as much as $169,602. Its not clear what they do, although they may be a form of upgrade. A sheriffs official in Michigan told the Detroit News last year that its not a tool to spy on people, unequivocally. But if thats the case, its hard to imagine why its purpose would be secretive.
Also Check: How To Enroll In The Police Academy
Sadly I Have Died Law Enforcement Wants To Unlock My Phone But They Cant Get My Password Due To My Aforementioned Death What Happens Now
Short answer: Your Fourth and Fifth Amendment rights generally end when you do. But other parties have rights, too, and those might be enough to keep the government out of your phone.
Long answer: This isnt about your Fourth or Fifth Amendment rights anymore for the most part, you lost those when you died. If law enforcement cant get into your device on its own, it may well be the phones manufacturers rights that come into question.
Attorney General Bill Barr has made no secret of his disdain for Apple over its refusal to grant law enforcement access to locked and encrypted devices. In May, he a legislative solution that would force tech companies to cooperate with his demands.
Barr also claimed in January that the only way the FBI could access dead suspected terrorist Mohammed Saeed Alshamranis iPhones is if Apple unlocked them. The agency has made this argument before. In 2016, the United States tried to use the All Writs Act, which dates back to 1789, to force Apple to create a back door that would give the FBI access to the San Bernardino shooters locked phone. Apple refused, saying the government could not force it to create a crippled and insecure product that it would not have built otherwise. So far, theres been no legal resolution: In both cases, the FBI was able to access the phone through other means before a court could rule on it.
How To Ping A Mobile Phone Location
by Ezekiel James / in Style
Mobile phone companies can locate a phone’s remote location through a process called “pinging.” What this basically means is that a mobile phone company can pinpoint your mobile phone’s location by locating the phone tower closest to where your cellular device most recently sent and received a signal. This is a very useful tool for police and rescue workers in locating criminal suspects, people who need urgent medical attention and missing persons. It is illegal, however, for a civilian to ping a phone she does not own.
Determine the mobile phone number you want to ping. Some mobile phone companies may require the serial number of the phone as well.
Contact the mobile phone provider associated with the mobile phone you want to ping. Ask the mobile phone company to ping the phone for you, and then provide the necessary information about the phone to the mobile phone company. Mobile phone providers have varying policies about how, when or if they ping mobile phones. Most mobile phone companies will not ping a phone that does not belong to you. The owner of the mobile phone will have to personally call the mobile phone provider and give the mobile phone company permission to let you ping the phone.
- Mobile phone companies can locate a phone’s remote location through a process called “pinging.”
- Ask the mobile phone company to ping the phone for you, and then provide the necessary information about the phone to the mobile phone company.
Related
Also Check: How Can I Get A Police Report